En Intcomex Cloud, nuestro objetivo es brindarte a ti, nuestro partner, las mejores soluciones en la nube, así como todas las herramientas que puedas necesitar para alcanzar el éxito. Con eso en mente, hemos creado una completa variedad de servicios de vanguardia para que satisfagas cada una de las necesidades de tus clientes.
Beyond Programa de Partner
Beyond refuerza la oferta de los partners con servicios de valor agregado, herramientas y conocimientos, logrando que los servicios relacionados con la nube sean rentables y fáciles de manejar apoyando su crecimiento.
Empower
Potencia tu negocio en la nube con nuestra plataforma de vanguardia diseñada para impulsar tus decisiones estratégicas y maximizar tus oportunidades comerciales.
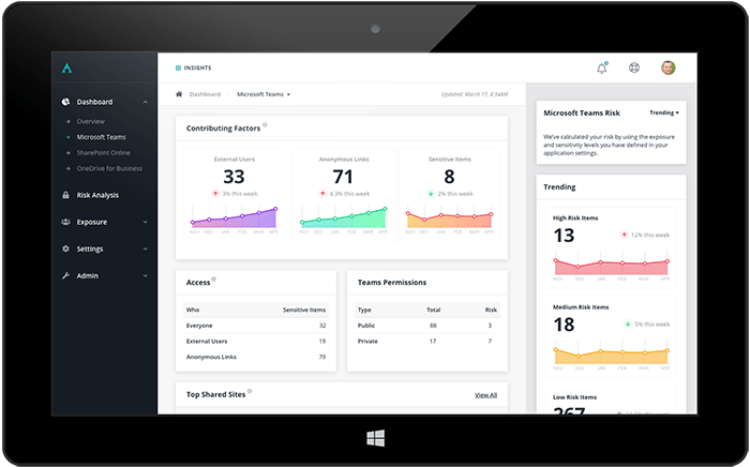
Insights
Nuestro programa ofrece cursos y mentorías especializadas para potenciar tus habilidades y brindar un servicio excepcional a tus clientes.
Innovadores Digitales
¿Quieres ser el próximo Unicornio?
Uno de los objetivos de cualquier nuevo desarrollo es ser relevante en el mercado. Intcomex pone a tu disposición nuestro equipo regional especializado en apoyar a empresas y soluciones como las tuyas a crecer en un mercado
Eventos
Tenemos un catálogo de eventos pensado en lo que nuestros partners quieren y necesitan para aprender nuevas habilidades, ampliar la experiencia y crear comunidad. No importa tu perfil, tenemos entrenamientos para todos los niveles de expertise.
Blog
Explora el universo de la tecnología en la nube con nosotros. Descubre artículos de interés, notas de prensa y las últimas novedades de la industria. ¡Conéctate con el futuro de la tecnología en la nube en Intcomex Cloud!
Casos de éxito
Aquellas empresas que han tomado la decisión de estar con nosotros, han vivido la experiencia de llegar más alto. Conoce un poco más de Intcomex Cloud a través de la experiencia de nuestros partners.
ICP: Intcomex Cloud Platform
Es la plataforma digital que Intcomex ha diseñado especialmente para ti, donde encuentras el más amplio portafolio de productos y servicios con procesos automatizados de venta, implementación y visibilidad de facturación que simplificarán tu trabajo.
Impulsa el crecimiento de tu software
Ayudamos a empresas emergentes y de software a posicionar y mejorar sus ventas a través de una plataforma tecnológicas de clase mundial (ICP), liberando tiempo valioso para resolver problemas del mundo real.
Mejora la rapidez y efectividad de Tus empleados y equipos de trabajo
Las herramientas en la nube para la colaboración en equipo facilitan la comunicación y rompen las barreras del espacio y del tiempo, permitiendo a los miembros de tu equipo comunicarse en cualquier momento y desde cualquier lugar.
Tus proyectos en las mejores manos
Te brindamos soluciones especializadas para el negocio respaldadas por nuestra experiencia en la nube. Busca en nuestro catálogo para encontrar exactamente lo que estás buscando.
Servicios Profesionales
Acelera tu negocio en la nube
Habilita tu transformación digital con servidores, software y otras soluciones de infraestructura de TI líderes para llevar tu negocio más allá
Impulsa el crecimiento de tu software
Ayudamos a empresas emergentes y de software a posicionar y mejorar su ventas a través de una plataforma tecnológicas de clase mundial (ICP), liberando tiempo valioso para resolver problemas del mundo real.
Todo lo que necesitas para administrar tu negocio correctamente
Toda empresa necesita algunos elementos básicos: correo electrónico, una suite ofimática, un lugar para almacenar archivos y una forma de compartirlos. Lo que hagas no importa, pero cómo lo hagas puede marcar la diferencia.
Mantenerse seguro en la nube
Protege tu entorno de ataques maliciosos, amenazas internas y errores humanos con soluciones de ciberseguridad líderes
![]()
![]()
![]()
Pon a salvo la información en caso de que haya algún problema
La velocidad de reacción ante imprevistos aumentará de manera considerable, así como la productividad de los empleados ya que no tendrán que duplicar su trabajo, lo que hará que los clientes tengan más confianza en la empresa.
![]()
![]()
![]()
Mejora la rapidez y efectividad de Tus empleados y equipos de trabajo
Las herramientas en la nube para la colaboración en equipo facilitan la comunicación y rompen las barreras del espacio y del tiempo, permitiendo a los miembros de tu equipo comunicarse en cualquier momento y desde cualquier lugar.
Beyond Partner Program
Beyond reinforces the offering of partners with value–added services, tools, and knowledge, making cloud–related services profitable and easy to manage, supporting their growth.
Empower
Boost your cloud business with our cutting-edge platform designed to drive your strategic decisions and maximize your business opportunities.
Insights
Our program offers specialized courses and mentorship to enhance your skills and provide exceptional service to your clients.
Digital Innovators
Do you want to be the next Unicorn?
One of the goals of any new development is to be relevant in the market. Intcomex puts at your disposal our regional team specialized in supporting companies and solutions like yours to grow in a market.
Events
We have an events catalog designed for what our partners want and need to learn new skills, expand their experience, and create community. No matter your profile, we have trainings for all levels of expertise.
Success Cases
Those companies that have taken the decision to be with us, have experienced the journey of reaching higher. Get to know more about Intcomex Cloud through the experience of our partners.
ICP: Intcomex Cloud Platform
Intcomex Digital Platform is the digital platform specially designed for you, where you find the widest portfolio of products and services with automated sales, implementation and billing visibility processes that will simplify your work.
Drive the growth of your software.
We help emerging and software companies to position and improve their sales through a world-class technology platform (ICP), freeing up valuable time to solve real-world problems.
Your projects in the best hands.
We provide specialized solutions for your business backed by our cloud experience. Look through our catalogue to find exactly what you‘re looking for.
Professional Services
At Intcomex Cloud, our goal is to provide you, our partner, with the best cloud solutions and all the tools you need to achieve success. With that in mind, we have created a complete range of cutting–edge services to meet each of your customers‘ needs.
We want to put our highly–rated cloud experts at your service, so you can make our experience and cutting–edge methodologies your own, and thus offer your clients a wide range of innovative consulting services.
Drive the growth of your software.
We help emerging and software companies to position and improve their sales through a world-class technology platform (ICP), freeing up valuable time to solve real-world problems.
All you need to manage your business properly
Every business needs some basic elements: email, an office suite, a place to store files and a way to share them. What you do doesn‘t matter, but how you do it can make a difference.
Stay safe in the cloud
Protect your environment from malicious attacks, internal threats, and human errors with industry–leading cybersecurity solutions.
Save the information in case of any problems.
The reaction speed to unexpected events will increase considerably, as well as the productivity of the employees since they will not have to double their work, which will make the customers have more confidence in the company.
Improve the speed and effectiveness of your employees and teams.
Cloud tools for team collaboration facilitate communication and break down space and time barriers, allowing members of your team to communicate at any time and from anywhere.